Introduction
The space sector of India has reached a historic inflexion point. Between government missions, commercial ventures, and dual-use applications, Indian satellites today power banking transactions, agricultural advisories, weather forecasting, disaster early-warning systems, military communications, and navigation. India is the world’s fourth-largest securities market, and its digital economy cannot function without orbital infrastructure.
The threat environment has evolved to match this dependency. During Operation Sindoor, India’s national networks experienced over 1.5 million cyberattack attempts, with attacks on government infrastructure surging nearly sevenfold. These were not random criminal probes. They were coordinated, state-grade disruption attempts targeting the very systems that India’s economy and national security now depend upon.
Against this backdrop, on February 26, 2026, the Indian Computer Emergency Response Team (CERT-In) and the Satcom Industry Association of India (SIA-India) jointly released the Cyber Security Framework and Guidelines for Space Including Satellite Communication India’s first comprehensive, sector-specific cyber defence mandate for space systems. This publication provides a complete legal analysis of the framework, its statutory basis, key provisions, compliance obligations, international comparisons, and strategic implications.
Framework Overview: CERT-In’s Mandate and Scope
The Issuing Bodies
The framework is a joint publication of:
- CERT-In (Indian Computer Emergency Response Team): established under the Ministry of Electronics and Information Technology (MeitY), functioning as India’s national nodal agency for cybersecurity incidents and response
- SIA-India (Satcom Industry Association of India): the apex industry body representing India’s satellite communication sector.
The decision to issue the framework as a public-private collaboration is deliberate. As SIA-India’s President Dr. Subba Rao Pavuluri, noted at the release event, “Public-Private Partnership and the considered views of industry are fundamental to strengthening cyber resilience across any sector.” This collaborative authorship reflects a consensus-building approach that mirrors international best practice.
Scope of the Framework
The framework covers the full value chain from space. Specifically, it applies to:
- Government entities: ISRO and affiliated agencies, defence satellite operations, government ground station operators
- Private satellite operators: communication, earth observation, navigation
- Ground segment operators: mission control centres, teleport facilities
- Equipment manufacturers and vendors: hardware and software suppliers to the space industry
- Private space enterprises and startups: all entities operating under IN-SPACe authorisation
- Satellite service providers: entities delivering connectivity, broadcasting, positioning, or remote sensing services
- User terminals and IoT operators: organisations deploying VSATs, satellite phones, or IoT devices using satellite connectivity
The framework’s philosophical architecture rests on what CERT-In Director General Dr. Sanjay Bahl described as “defence in depth, breadth, and height” layered protection not merely against known threats, but against the full spectrum of emerging and unanticipated attack vectors.
Legal Basis and Statutory Authority
Primary Statutory Foundation
The framework derives its authority primarily from Section 70B of the Information Technology Act, 2000, which constitutes CERT-In as the national authority for cybersecurity incidents and empowers it to issue directions, guidelines, and advisories to organisations across sectors. CERT-In’s 2022 Cybersecurity Directions (issued under the same Section 70B authority) established the precedent of sector-specific, mandatory compliance obligations for cybersecurity, including the controversial logging and breach-reporting requirements for VPN providers and data centres.
Supplementary Legal Framework
The space framework does not operate in isolation. It functions within and must be read alongside a wider constellation of legal instruments:
- The Indian Space Policy 2023: Released in April 2023, this policy opened India’s space sector to private participation and designated IN-SPACe (Indian National Space Promotion and Authorisation Centre) as the single-window regulatory and authorisation body for all space activities, both governmental and commercial. Section 4 of the Policy imposes security-related obligations on all authorised entities, creating a platform for integrating cybersecurity compliance into licensing conditions.
- The IT Act, 2000: Sections 66, 66B, and 70A–70B provide a criminal and regulatory basis for prosecuting cyber offences affecting critical infrastructure, including space systems. Section 70A empowers the government to designate critical information infrastructure (CII); breaches of CII are subject to enhanced penalties.
- The DPDP Act, 2023: To the extent that space systems process personal data (e.g., location data, user communications), the framework must be read in light of the DPDP Act’s obligations on data fiduciaries, including consent, storage limitations, and breach notification.
Advisory vs. Mandatory Status
A key legal point for compliance teams: as of February 2026, the framework is advisory in nature. It does not carry the binding legal force of a CERT-In Direction issued under Section 70B. However, two mechanisms exist that could rapidly change this status:
- CERT-In Directions: CERT-In can elevate specific provisions to binding directions at any time under Section 70B, as it did with the 2022 Cybersecurity Directions.
- IN-SPACe Licensing Conditions: IN-SPACe may incorporate framework compliance as a condition of space activity authorisation, creating de facto mandatory obligations for all licensed operators.
The prudent legal position is to treat the framework as prospectively mandatory and begin compliance planning immediately.
Key Provisions Breakdown
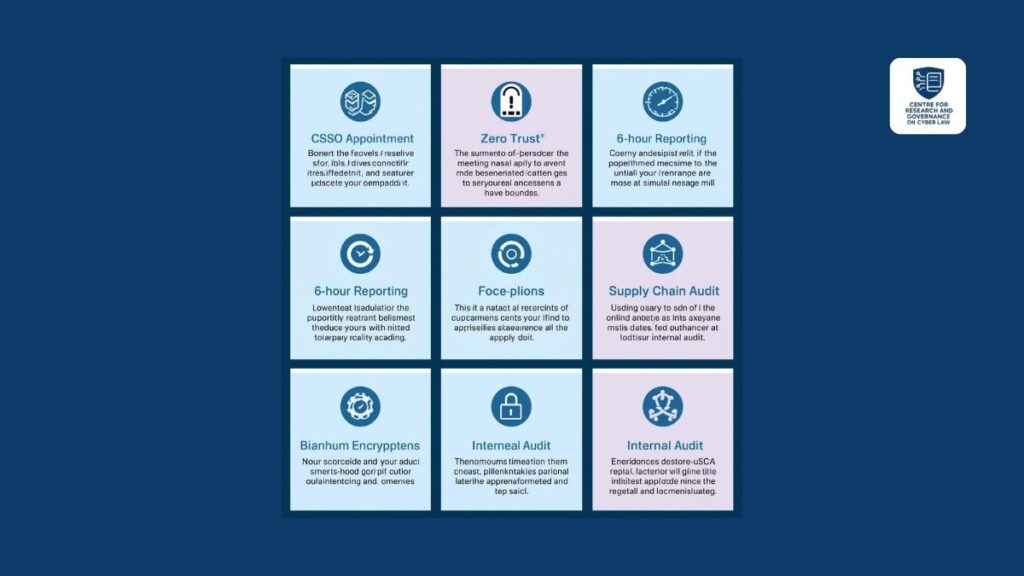
Chief Satellite Security Officer (CSSO)
The most structurally significant provision of the framework is the mandate to appoint a Chief Satellite Security Officer (CSSO). The CSSO is the designated individual responsible for:
- Overseeing the organisation’s entire cybersecurity governance framework for space operations
- Ensuring ongoing compliance with framework guidelines and any subsequent CERT-In directions
- Serving as the primary point of contact for CERT-In in incident response and coordination
- Leading and being accountable for internal and external compliance audits
This role is modelled conceptually on the Chief Information Security Officer (CISO) role required under the IT (Intermediary Guidelines and Digital Media Ethics Code) Rules, 2021, and the Data Protection Officer (DPO) under the DPDP Act framework, but with domain-specific responsibilities uniquely applicable to satellite operations. The appointment is not merely administrative; it creates personal accountability for cybersecurity governance, mirroring global best practice in regulated sectors.
Segment-Wise Security Architecture

The framework mandates security controls at four distinct operational segments:
| Segment | Description | Key Requirements |
| Space Segment | The satellite and its payload in orbit | Secure firmware, authenticated command interfaces, tamper-resistance |
| Ground Segment | Mission control and ground stations | Access controls, intrusion detection, physical and logical security |
| Communication Links | Uplink and downlink channels | Encrypted signal transmission, anti-jamming, anti-spoofing measures |
| User Segment | Terminals, VSATs, IoT devices | Device authentication, secure boot, network isolation |
This segment-wise approach mirrors the structure advocated by the US Space Policy Directive-5 (September 2020), which specified protection requirements for each layer of the space system architecture.
Quantum-Resistant Encryption
The framework recommends transitioning to post-quantum cryptography (PQC) encryption algorithms designed to withstand attacks from quantum computers. This recommendation does not arise in isolation. CERT-In and SISA released a dedicated Quantum Cyber Readiness Whitepaper in July 2025, laying out India’s migration roadmap from classical to quantum-resistant cryptographic standards.
The strategic rationale is pressing: nation-state adversaries are known to engage in “harvest now, decrypt later” operations, collecting encrypted transmissions today with the intention of decrypting them once sufficiently powerful quantum hardware becomes available. For satellite command-and-control data, which may remain sensitive for decades, this is not a future risk; it is a present one.
Incident Reporting Timeline
Organisations must report cybersecurity breaches, anomalies, and significant incidents to CERT-In within 6 hours of detection. This aligns with the 6-hour reporting requirement established for all regulated entities under the CERT-In Cybersecurity Directions, 2022. For space systems, the rationale for rapid reporting is especially compelling: a satellite under a command-hijacking attack can be rendered permanently non-operational within minutes, and cascading effects on other systems can occur even faster.
Zero Trust Architecture
The framework mandates adoption of Zero Trust principles—an approach premised on the assumption that no user, device, or system is inherently trustworthy, whether inside or outside the network perimeter. Every access request must be continuously authenticated, authorised, and validated. For satellite operations, where a compromised insider with ground station access could issue destructive commands, Zero Trust provides a critical layer of control.
Supply Chain Security
Given the increasing globalisation of space hardware manufacturing, supply chain risk is an acknowledged vector for attacks. The framework requires operators to maintain detailed records of hardware components, source equipment from trusted and verified vendors, and conduct structured vendor risk assessments. This provision directly addresses the threat of counterfeit or tampered components entering India’s space infrastructure through global supply chains.
Audit Requirements
To ensure ongoing compliance rather than one-time implementation:
- Internal audits: Every 6 months
- External (third-party) audits: Once annually
The CSSO is accountable for both audit cycles. Audit findings must be documented and remediated within defined timeframes.
Compliance Obligations for Different Entities
Government Space Agencies (ISRO, DRDO, Defence)
These entities are already subject to existing government cybersecurity protocols, but now have a structured, sector-specific framework to comply with. The CSSO requirement adds a new governance layer. Incident reporting obligations apply equally, with the added dimension that government agencies may have parallel classified reporting requirements under defence protocols.
Licensed Private Satellite Operators
Private operators authorised by IN-SPACe bear the full weight of compliance obligations. They must: appoint a CSSO; implement segment-wise security controls; establish 6-hour incident-reporting pipelines to CERT-In; commence quantum-encryption planning; conduct supply-chain audits; and schedule the mandated audit cycle. These obligations represent a significant operational investment, particularly for smaller new-space companies.
Space Technology Startups
India’s burgeoning new-space startup ecosystem, comprising over 300 registered entities faces a compliance challenge. While the framework’s security requirements are technically sound, the capital costs of implementing quantum-resistant encryption, maintaining audit programs, and appointing senior security leadership are material. Policy recommendation: CERT-In and IN-SPACe should consider a tiered compliance timeline for startups, similar to the phased approach adopted in DPDP Rules 2025.
SatCom Service Providers and IoT Operators
Entities providing satellite connectivity services, including rural broadband operators, maritime and aviation connectivity providers, and IoT platform operators using satellite backhaul, are within scope. For many, this will require significant technical upgrades to user terminals and ground infrastructure.
Penalties and Enforcement Mechanism
Current Enforcement Gap
As of its February 2026 release, the framework does not specify a standalone penalty schedule. This is a notable limitation. Without defined penalties, enforcement remains reliant on existing statutory mechanisms.
Under the IT Act, 2000:
- Section 70: Unauthorised access to “protected systems” (which can include designated space infrastructure): imprisonment up to 10 years
- Section 70B (non-compliance with CERT-In directions): once directions are issued, penalties apply under IT Act provisions
- Sections 43 and 66: Computer-related offences, including unauthorised access, damage, and disruption: penalties up to ₹5 crore (civil) and 3 years imprisonment (criminal)
Under Indian Space Policy 2023 / IN-SPACe Authorisation:
Non-compliance with authorisation conditions which may be amended to incorporate framework requirements, can result in suspension or cancellation of the space activity authorisation, effectively shutting down operations.isro+1
Expected Evolution
Legal practitioners should anticipate:
- CERT-In issuing binding Section 70B Directions for space sector entities, carrying explicit compliance deadlines and penalties
- IN-SPACe integrating framework compliance as mandatory licensing conditions in authorisation renewals and new applications
- A dedicated Space Activities Act (long discussed but not yet enacted), potentially codifying cybersecurity obligations with sector-specific penalties
International Comparison
United States: Space Policy Directive-5 (2020)
The US issued Space Policy Directive-5 (SPD-5) in September 2020, becoming the first country to establish a comprehensive cybersecurity policy framework specifically for space systems. SPD-5 established five foundational principles:
- Risk-based, cybersecurity-informed engineering throughout the space system lifecycle
- Development and implementation of cybersecurity plans for all space systems
- Protection of command, control, and telemetry links through authentication and encryption
- Adoption of NIST Cybersecurity Framework practices for ground systems
- Management of supply chain risks through trusted sourcing and tracking.
Comparison with India’s Framework: India’s 2026 framework closely mirrors SPD-5’s architectural approach (segment-wise security, supply chain focus, encryption) while adding operationally specific mandates (CSSO appointment, 6-hour reporting timelines, Zero Trust) that SPD-5 left to agency discretion. India’s framework is therefore arguably more prescriptive and implementation-focused than SPD-5.
European Union: Space Strategy for Security and Defence (2023)
The EU presented its Space Strategy for Security and Defence in March 2023, with implementation measures developed through 2024. Key elements include:
- Expanding threat response mechanisms (initially covering Galileo navigation) to all EU space systems and services
- Establishing a dedicated EU Space Information Sharing and Analysis Centre (EU Space ISAC) for threat intelligence sharing.
- Conducting space exercises to test collective response capabilities
- Fostering collaboration between space and defence
Comparison with India’s Framework: The EU approach is more institutionally collaborative (emphasising information sharing across member states and public-private coordination), while India’s framework is more operationally prescriptive (specifying roles such as the CSSO, audit cycles, and reporting timelines). The EU strategy also has a stronger dual-use/defence dimension, reflecting the EU’s distinct institutional framework.
The Global Landscape
| Country/Bloc | Framework | Key Features |
| USA | SPD-5 (2020) | Risk-based engineering, NIST alignment, supply chain |
| EU | Space Strategy for Security & Defence (2023) | Collective response, threat sharing, EU Space ISAC |
| India | Space Cyber Security Framework (2026) | CSSO, Zero Trust, 6-hr reporting, quantum-ready |
India has entered this space six years after the US and three years after the EU, but with a framework that reflects lessons learned from both precedents.
Challenges and Implementation Roadmap
Key Implementation Challenges
1. Regulatory Fragmentation
Multiple regulators have jurisdiction over overlapping aspects of space cybersecurity: CERT-In (cyber incidents), IN-SPACe (space activity authorisation), MeitY (digital policy), Ministry of Defence (dual-use systems), and the Department of Space. Clear inter-agency coordination protocols are essential but currently undefined.
2. Talent Gap
Appointing a qualified CSSO requires personnel with rare expertise spanning satellite operations, cybersecurity architecture, and regulatory compliance. India’s space sector will need to urgently develop this talent pipeline.
3. Legacy Systems
Many existing satellites and ground stations were designed and deployed before modern cybersecurity requirements existed. Retrofitting security controls, particularly quantum-resistant encryption on legacy orbital hardware, is technically complex and expensive.
4. Startup Ecosystem Pressure
India’s 300+ new-space startups lack the compliance budgets of established operators. A tiered implementation timeline and government-supported compliance assistance would significantly improve adoption.
5. Advisory-to-Mandatory Transition Uncertainty
Without a clear timeline for when advisory provisions become binding, organisations face the familiar challenge of “anticipatory compliance”, investing resources based on uncertain future obligations.
Recommended Implementation Roadmap
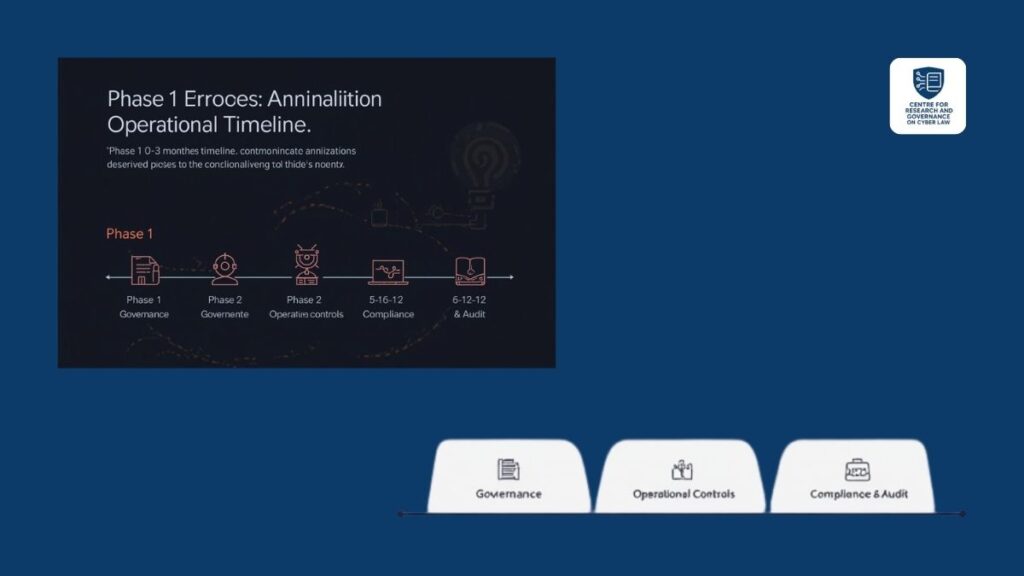
Phase 1 (0–3 months): Governance
- Designate CSSO (or acting equivalent pending formal requirement)
- Conduct gap analysis: current security posture vs. framework requirements
- Map supply chain: identify all hardware vendors and data flows
Phase 2 (3–6 months): Operational Controls
- Implement segment-wise security controls across space, ground, communication, and user segments
- Establish CERT-In 6-hour incident reporting pipeline
- Initiate Zero Trust architecture review
Phase 3 (6–12 months): Compliance & Audit
- Schedule the first internal audit
- Begin quantum-resistant cryptography migration planning (timeline: 18–36 months)
- Engage external auditors for annual review
- Review vendor contracts for supply chain security clauses
Implications for India’s Space Sector
The framework arrives at a moment of extraordinary momentum for India’s space economy. India’s space sector currently contributes significantly to GDP, and projections for private sector growth over the next decade are substantial. IN-SPACe has authorised dozens of private entities, satellites are being launched commercially, and Indian startups are attracting global investment.
Cybersecurity governance, done well, is a strategic enabler of this growth, not an obstacle. Foreign customers, partners, and investors in Indian space ventures will increasingly demand verifiable cybersecurity compliance as a condition of commercial relationships. The framework positions India to compete credibly on the global stage for satellite service contracts, data partnerships, and joint ventures.
Simultaneously, the framework signals India’s strategic intent: space is now formally treated as critical national infrastructure, and attacks on it will be met with the full weight of India’s cybersecurity and national security apparatus. This deterrence signal has value beyond compliance; it communicates to state and non-state adversaries that India’s space architecture is hardened, monitored, and actively defended.
Conclusion: Future Outlook
The India Space Cyber Security Framework 2026 is a landmark document. It is India’s first serious, comprehensive attempt to address the full spectrum of cyber threats to national space infrastructure. By mandating clear governance structures (CSSO), operational requirements (segment-wise controls, Zero Trust), procedural obligations (6-hour reporting, audit cycles), and forward-looking technical standards (quantum-resistant encryption), it establishes a credible foundation for secure, resilient space operations.
The framework’s current advisory status will evolve. CERT-In’s track record escalating from voluntary guidelines to binding Section 70B Directions, as seen in 2022, strongly indicates that space sector entities should treat compliance planning as an immediate priority rather than a deferred obligation.
Three policy developments warrant close monitoring:
- Dedicated Space Activities Act: Legislation has been discussed but not enacted. If passed, it could codify cybersecurity obligations with statutory penalty structures.
- IN-SPACe Licensing Integration: Watch for amendments to authorisation conditions that incorporate framework compliance.
- CERT-In Directions for Space Sector: A binding direction under Section 70B—specifying compliance deadlines and penalties could be issued at any time, as was done for the financial sector and internet service providers in 2022.
For India to realise its ambition of becoming a global space power, security and sovereignty in the orbital domain must be as robust as its launch capabilities. The 2026 framework is the legal and operational foundation for that security. The challenge now is implementation.
This analysis is prepared for educational and informational purposes by the Centre for Research and Governance on Cyber Law (CRGCL). It does not constitute legal advice. For specific compliance requirements, consult qualified legal counsel.